SSL Gateway
Objective
The objective of the SSL Gateway is to deliver a secure Remote Desktop session between any location in the world and an AADS Terminal Server. The term “secure” implies:
- Strong SSL encryption is used in order to avoid “listening” on the connection. The RDP-protocol in itself is already encrypted, but a SSL encryption beneath the RDP connection, using strong certificates, will do a much better job.
- Identification of both the client and the server. The SSL Gateway gives an Administrator the possibility to deliver specific Client Builds with an included certificate, which can only connect to 1 or more AADS Terminal Servers. Also, the Administrator can “withdraw” a Client certificate, such that the client can not connect any more.
Specifications
- The Certificates generated by the SSL Gateway are based on RSA, 4096 bits.
- Encryption Cipher: TLS_CHACHA20_POLY1305_SHA256:TLS_AES_256_GCM_SHA384, TLSv1.3
- Optional, because of "old" Client Devices: Encryption Cipher: ECDHE-ECDSA-AES256-GCM-SHA384 TLSv1.2
- Both the Client and the Server do verify each other certificate.
- The SSL Gateway can be used in an AADS Farm.
About the SSL Certificates
-
Using AADS Maintenance & Control, the AADServer generates all SSL Certificates.
-
Each AADServer in the world generates its own unique SSL Server and Client Certificates.
-
There is NO dependency on any other party in the world who sells, distributes, verifies or signs SSL Certificates.
-
The encryption between the Clients and the Server is end-to-end encryption and includes verification about which Client is connecting with which Server.
-
Nobody / nothing else in the world can decrypt the communication between your AADServer and your AADS Clients using the SSL Gateway.
For example, when it is about SSL Certificates and browsers, the problem can exist that, if a so called SSL Certificate Signing Authority is compromised or abused, the encryption between the browser and the webserver can be decrypted by a third party or hacker:
The problem of a "Certificate authority compromise" does not exist when using the AADS SSL Gateway, because the AADServer is completely independent when it is about the SSL Certificates. Nobody / nothing can decrypt the SSL Connection, except the AADServer and the Client PC's.
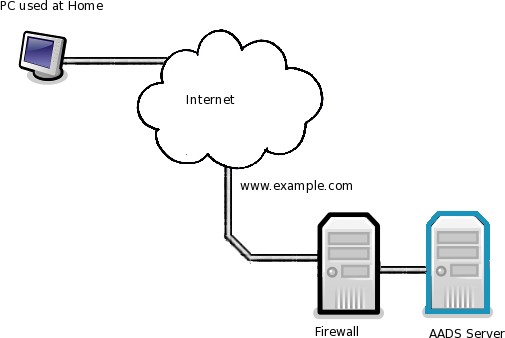
Example 1: Stand Alone AADS Terminal Server
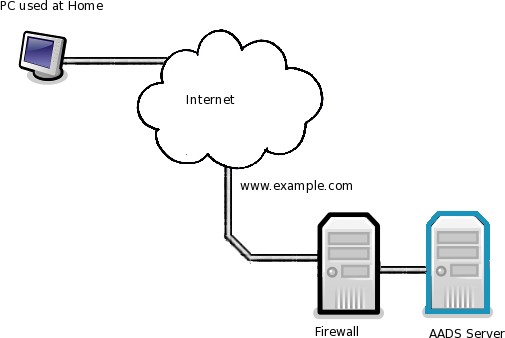
- The company has a connection with the internet. This connection is reachable by the domain name www.example.com
- The client using the home PC connects using www.example.com:3443.
- The Firewall does forward incoming connections for port 3443 to the AADS Terminal Server.
- The AADS Terminal Server is running the SSL Gateway on port 3443.
- It is a stand-alone AADS Terminal Server; there is no AADS Farm.
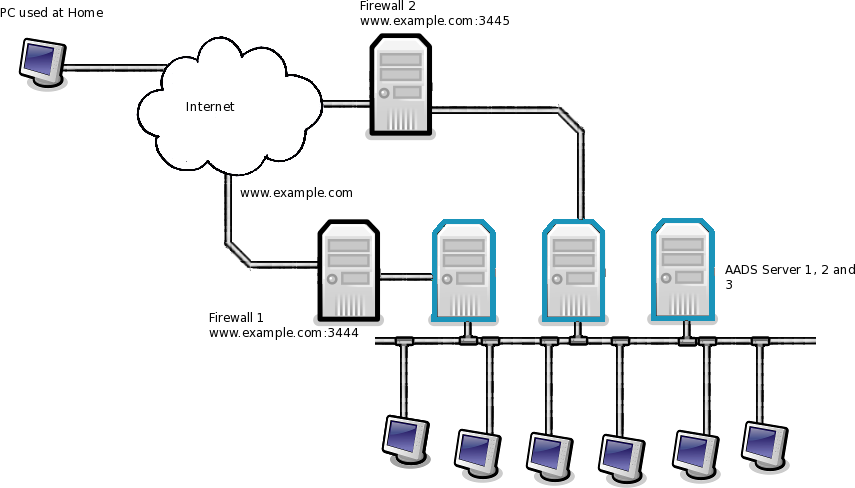
Example 2: AADS Farm with 3 Terminal Servers and 2 internet connections
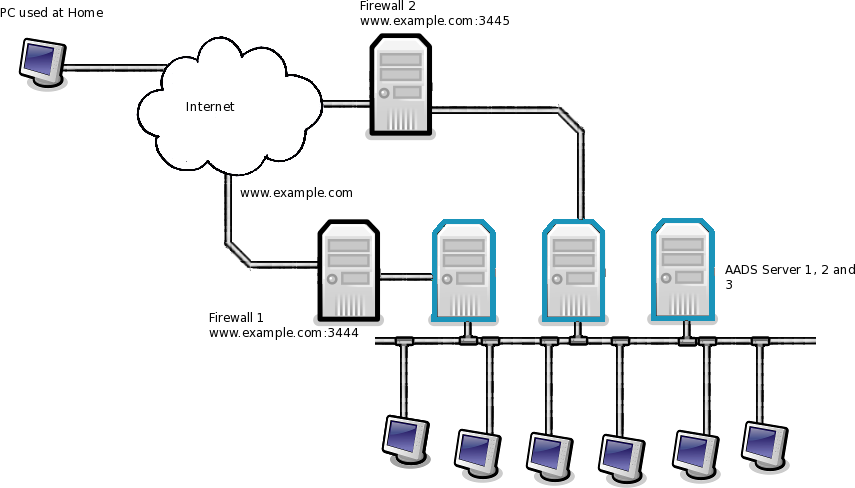
- The company has 2 connections with the internet.
- When a client tries to connect to www.example.com:3444, the connection goes through the Firewall 1.
- When a client connects using www.example.com:3445, the connection goes through the Firewall 2.
- The client at the Home PC can use either www.example.com:3444 or www.example.com:3445
- By offering client 2 connection addresses, and having 2 connections with the internet, the company can offer the client redundancy for the connection to the AADS Farm.
- Firewall 1 forwards port 3444 to the SSL Gateway on AADS Terminal Server 1.
- Firewall 2 forwards port 3445 to the SSL Gateway on AADS Terminal Server 2.
- The SSL Gateways on both AADS Terminal Server 1 and 2 will handle the correct forwarding to the appropriate AADS Terminal Server in the Farm, based on the Load Balancing Parameters.
- AADS Terminal Server 3 does not run the SSL Gateway.
|
© 2012-2023 AADS WorldWide. Terminal Server | Application Server | Remote Desktop solutions | Firewall
|

|

|

|
|